2020 brought on a lot of cyber attacks and cyber attack techniques, in this weeks blog, we cover 3 of the top lures unleashed on the
unsuspecting public during one of the most unprecedented years in living memory.
COVID-19 Information
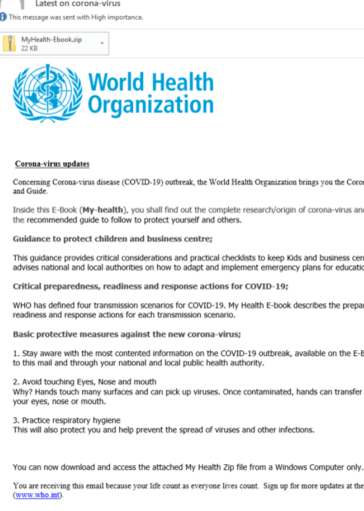
February 2020 saw the initial stages of the COVID-19 coronavirus being used as a lure for unsuspecting email recipients and website
visitors.
An example to the left is where branding from the World Heath Organisation (WHO) was used as bait in email phishing attacks with malicious attachments parading as Coronavirus updates and safety guides to the public desperate for updates on the as then mysterious illness.
The attachments of course, were malware designed to infiltrate the victims device and do untold damage.
Another attack vector used was malicious websites like below, purporting to hold the "best possible protection" against COVID-19. Again, members of the public were preyed on for seeking information about the virus.

Online store credit card skimming
 COVID-19 also brought about the move to online trading for a number of retail stores and restaurants, some even making the move to online
exclusively as local government laws prevented them from opening their bricks and mortar stores to the public.
COVID-19 also brought about the move to online trading for a number of retail stores and restaurants, some even making the move to online
exclusively as local government laws prevented them from opening their bricks and mortar stores to the public.
Where online shopping increased, so did attempts to steal online credit card data. Whilst this method of cyber attack is not a new one it certainly opened up a greater number of opportunities for exploitation by cybercriminals, particularly if a store was new to online trading, perhaps their security features weren't as robust as they should be to prevent attacks.
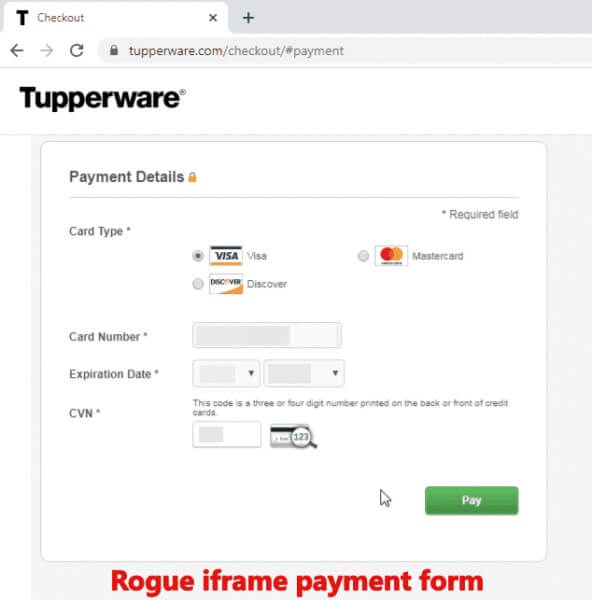
An example of a pre-existing online store targeted by attackers during the early months of COVID-19 was storage giant Tupperware, with a lot of workers now based at home undertaking DIY and organisation projects, businesses like Tupperware experienced an increase in website traffic. Cyber criminals jumped on this opportunity by inserting a malicious code into their primary website that would trigger a fraudulent payment form during the checkout process.
To unsuspecting users, the cyber heist was nearly undetectable. Upon trying to checkout from Tupperware’s online store, victims would first be shown a fraudulent, convincing payment form that asked for their credit card number, expiration date, and three-digit security code.
After victims confirmed their credit card details, they then received a warning notice that the website had timed out, and that they had to enter their credit card details a second time. Though this second payment form was actually legitimate, it was too late—the cyberthieves already had what they wanted, valid credit card details they could then sell on the dark web or use to make purchases.
The Tupperware attack was just one of many similar attacks in 2020. In fact, in March alone, Security software vendor Malwarebytes recorded a 26 percent increase in credit card skimming attacks compared to the month earlier
Imposter websites
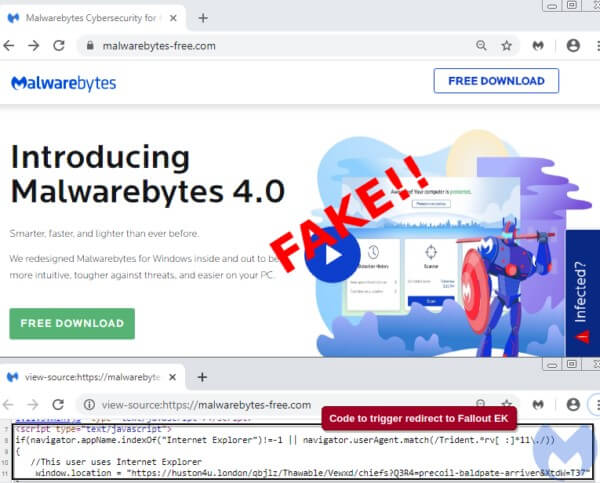 In April 2020, Malwarebytes themselves experienced the threat of an imposter website, their team discovered that a group of threat actors
had built a malicious website meant to serve as a gate to an exploit which would unleash an information stealer to visitors.
In April 2020, Malwarebytes themselves experienced the threat of an imposter website, their team discovered that a group of threat actors
had built a malicious website meant to serve as a gate to an exploit which would unleash an information stealer to visitors.
The malicious domain, at malwarebytes-free[.]com, presented users with much of the same information that the Malwarebytes website
homepage, in a cheeky move they had simply copied and pasted the text and images from the genuine site verbatim.
The domain was registered on March 29 2020 and was hosted in Russia.
When Malwarebytes were made aware of the site they looked closer, and found a short piece of JavaScript on the copycat site that checked a user’s web browser. If the user was visiting the site on Internet Explorer, they would be led to a malicious URL which belonged to the exploit kit.
If 2020 is anything to go by, 2021 will no doubt bring many more scams and cyber attacks and end users will need to remain vigilant. Why
not check out some of our previous blogs for tips on how to keep your data safe:
David speaks: Email antispam
and phishing
Phishing
Attacks: How scammers reel you in and what to do about it
How to
Protect Your Business from Ransomware