In mid-2020, the Australian Cyber Security Centre (ACSC) released their Annual Cyber Threat Report. This report was the result of data gathered from the tens of thousands of cyber security and cyber crime incidents the Centre responded to over the past 12 months. This post, and several of the next, will dive into the main threats reported by the ACSC, starting with the most common one: phishing and spear phishing.
“I fell for a phishing scam.”
“Phishing scam, what did they do?”
“I accidentally clicked on a link.”
These are just three examples of people who inadvertently fell for a phishing email. All three were from a Subreddit dedicated entirely to phishing. And you’ve probably heard the horror stories, if you haven’t been unlucky enough to fall for a phishing scam yourself.
But what exactly is phishing? How does it work? And most importantly, how do you spot a phishing attack before you fall for one?
That’s what this post is all about.
Clickety-Clickety, That’s All Folks: Phishing Subject Lines Most Often ClickedAccording to a TechRepublic article, these were some of the most “successful” subject lines used in phishing emails to get unsuspecting victims—both non-technical AND technical—to open it up.
|
What Is Phishing?
Here’s the short answer: phishing is a cyber crime where someone poses as a legitimate authority, person or organisation in order to get
people to hand over sensitive data.
Of course, there’s a lot more to phishing than that drab definition.
It usually turns up as email… but not always
Being so ubiquitous, email is a favourite delivery method for cyber attackers. In fact, 92% of all malware is delivered via email, so it’s not just phishing that takes advantage of this.
That said, in our increasingly mobile age, phishing can also take the form of text messages—again using a link to take people to a site ready to steal their details—or even phone calls, which may simply ask for credentials straight up.
Phishing can be targeted OR untargeted
We often think of phishing as someone putting together an email (and landing page) to steal credentials, and then sending it out en-masse, but it’s not always the case. Verizon’s 2017 Data Breach Investigations Report stated that 28% of phishing breaches were targeted cases… meaning the scammers set their sights on a specific person or business. (See more about spear phishing below.)
The finance industry is a prime target
Naturally, money is a main motivator behind any type of cyber crime (71% if you ask Verizon for an exact number) and it’s no different with phishing. So it makes sense that as far as phishers go, the finance industry has a target on its back.
How Does Phishing Work?
The panic of clicking what you suddenly realise is a phishing email is real… but the damage isn’t often done at that point. Here’s how a
typical phishing scam works.
1. A phishing email lands in your inbox
Sophisticated spam filters make sure you don’t see most of these email attempts, and even when a few do slip through the cracks, many are laughable in their “authenticity”. However, phishing emails can be sophisticated and appear completely legitimate, leading to unsuspecting users to take the email seriously.
2. You click on the link in the email
Phishing emails need to get you to a site where they can steal your details. So, they often have a serious and urgent “call to action” and a link for you to click on. This call to action can be to read an important message or update your details, and sometimes threatens dire consequences if you don’t act.
3. You land on a bogus website or landing page
Clicking the link isn’t fatal (however, see below). Usually you land on a bogus website that’s set up to match the email and appear authentic, but the purpose is to steal your details.
4. You enter sensitive details
“Logging in” means entering your username and password… and that’s when the scammers get you. The ACSC report shared a story of a woman who got an email from her bank to investigate suspicious transactions. She clicked the link, “logged in” to the fake website, and then shared details like DOB, credit card and Medicare details. Within a couple of hours, the criminals used those details to open three credit card accounts and rack up $30,000 in debt.
A Sneaky Alternative To Detail-Stealing WebsitesWhile websites are the most popular way scammers use to get your details, keyloggers are another method they can use to steal your details.A keylogger is a piece of malware that’s secretly installed onto your computer when you click a link or open an attachment from a phishing email. The keylogger then sits in the background of your computer, recording every keystroke you make and sending it to the hackers. They then sift through the data to pinpoint your log-in and other private details. |
Telltale Signs Of A Phishing Email
Here’s an example of a “great” phishing email:
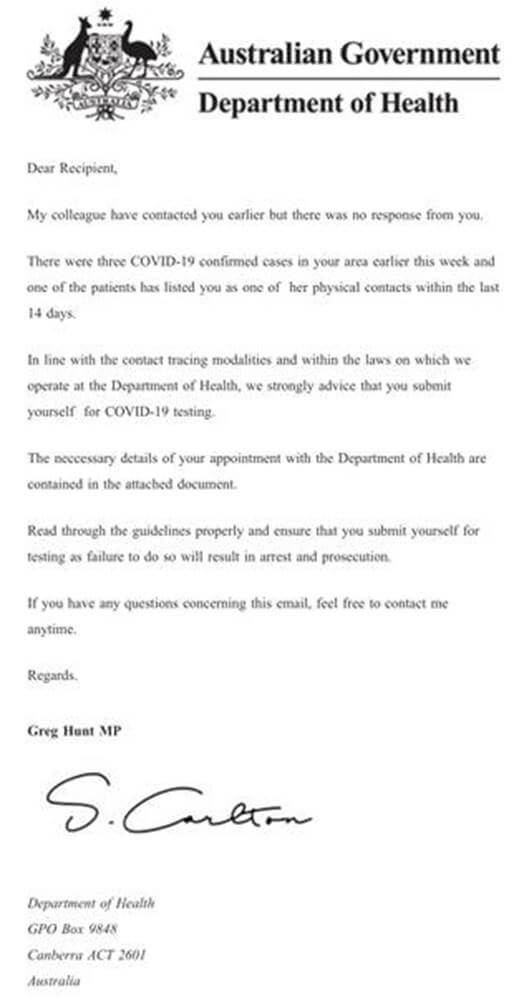
(Source: Scamwatch)
There’s no sloppy formatting. It’s from a seemingly credible source. Even the address at the bottom of the email is the actual email for the
Department of Health
But there ARE some giveaways:
- There are small grammar errors (“My colleague have contacted you…”)
- The signature clearly doesn’t match with the sender’s name
- There are no specific details or personalisation
- It asks the reader to open up an attachment (which is the same as clicking a link)
Of course, every phishing email is different. Some range from hysterically bad to almost perfect imitation. So what should you be looking for when a not-quite-right email arrives?
Here’s a checklist to help you spot a phishing email.
Sender name: always check that whoever is sending the email is familiar.
Sender domain name: this is the second half of the email address (i.e. the @test.com part of [email protected]). Sometimes this can be very similar if the scammer’s have done their homework.
Asks you to click a link or open an unknown attachment: if the message prompts you to open an attached file or click a link, think twice unless you trust the sender.
|
TIP: if the email asks you to click on a link, hover your mouse cursor over the link WITHOUT clicking. If the URL that
shows up is a long, jumbled mess, chances are it’s a phishing site. |
Spelling and grammar: poor spelling and grammar mistakes are often dead give-aways of a phishing email (though
unfortunately, it’s how a lot of us write emails too!)
Too good to be true: if an email turns up offering you a fantastic deal, don’t automatically believe it. Plus, a common tactic of phishers is to include an element of urgency, so if this fantastic deal is expiring in a matter of hours, be on your guard.
Confirmation requests: sure, you can get these from time to time, but be careful with any emails asking you to validate personal info or login details.
Unusual formatting: this one is often a dead give-away. Any email that looks like a five-year old formatted it is quite possibly a poor attempt at phishing.
Source doesn’t match the email: if an email says it’s from a trusted business or government organisation but the email is from somewhere like Gmail… it’s 99.9% a phishing email.
Spear Phishing: Net Vs Fishing Line
Phishing is basically casting a massive net out into the ocean with the intent of catching any old fish you come across. Criminals will send a phishing email in its thousands or millions and hope to catch a few people out. On the other hand, spear phishing is like stalking a prize fish with a state-of-the-art fishing line. It’s a carefully prepared operation aimed at just the one individual or organisation. The “reconnaissance” before launching the attack is actually the most important part of a spear phishing campaign, as it gives the criminal a credible narrative to use in the email. So, if you’re in their sights, they’ll stalk you on LinkedIn, Facebook, Twitter, and any other social media, to build up a profile of who you are. They might even do web searches to glean any other tid-bits. They cyber criminals then pose as you to send an email to one of your subordinates. They might ask to make an urgent transfer to a certain account; one they control. And all it takes is one careless moment or inattentive read of the email, and someone has transferred thousands of dollars directly to the criminals. Oh, and if you think you (or anyone else in your business) wouldn’t fall for this, think again. An experiment done by US security firm Rapid 7 ran a spear-phishing simulation that caught out 57% of the CEOs who volunteered to take part. |
Phishing Is Here To Stay
Sadly, phishing isn’t going anywhere.
In fact, it seems to only get more prevalent, with 55% of organisations surveyed in ProofPoint’s 2019 “State of the Phish” report advising they’d fallen victim to at least one phishing attack throughout the year.
With prevention being out of reach, it’s a matter of watchful observation and quick detection when a phishing email slips past the mail and spam filters. And fortunately, people are heeding the lessons: click rates dropped from 25% to 3% between 2012 and 2018 (obviously more needs to be done in this area if so many organisations fell prey to an attack).
However, if you and your team follow the checklist above, you’ll spot all but the most sophisticated phishing attacks sent your way and prevent any serious damage being done.
In the next of our ACSC series, we’ll be exploring another threat that too many businesses are familiar with: ransomware.
