Protect your business with expert penetration testing services.
Wouldn’t you like to uncover and fix vulnerabilities now, instead of paying thousands to recover from a breach later?
Cyber threats evolve daily, and a single vulnerability can lead to data breaches, compliance failures, and reputational damage. Our
penetration testing and vulnerability assessment services give you clear visibility into your risks—so you can fix them before attackers
exploit them.
Businesses in Brisbane and across Australia face increasing cyber risks. A vulnerability scan or penetration test identifies weaknesses in your network, applications, and portals. Whether you need a compliance penetration test, a portal security test with login access, or a network vulnerability scan, we provide actionable insights to strengthen your defenses.
Our penetration testing services include:
-
External Vulnerability Scan - Scanning of public-facing assets for known vulnerabilities and misconfigurations. Ideal
for routine security hygiene. From
$1,950 + GST per IP/Hostname.
-
Penetration Test (Unauthenticated) - Simulated attack without credentials to assess external exposure. Perfect for
compliance audits and assurance. From
$3,750 + GST.
-
Authenticated Penetration Test - Testing with login access for portals or apps to uncover deeper risks like broken access
controls and data exposure. Recommended for critical applications and pre-launch checks. From
$5,250 + GST.
- Detailed Reporting - Risk-ranked findings, remediation steps, and compliance-ready documentation.
- Retesting - Free re-testing within 14 days.
Don’t wait for a breach to expose your business. Undertaken by GIAC Penetration Tester (GPEN) qualified staff who compile detailed reports with quantifiable actions to take, our penetration testing services help you uncover vulnerabilities, so that you can fix them fast, and stay compliant with confidence.
Book your test today and take the first step toward a more secure future.
"After completing a penetration test with FortiTech, we uncovered several vulnerabilities we didn’t know existed. Their clear reporting and guidance made it easy to fix issues quickly, and now we feel far more confident about our security posture.."
Sarah Mitchell, IT Manager, Hastings Legal Group
|
|
PROACTIVE SECURITY Stay ahead of cyber threats by identifying and fixing vulnerabilities before attackers exploit them. Our penetration testing simulates real-world attack scenarios, giving you the insight to strengthen your defenses before it’s too late. |
Why Businesses Are Choosing Our Penetration & Vulnerability Testing
From external vulnerability scans to full penetration tests, we deliver a complete solution to uncover and address security gaps before attackers exploit them. Our testing approach ensures we stay ahead of evolving cyber threats, giving your business the confidence it needs to operate securely. Gain access to clear, actionable reports and expert guidance—without unnecessary complexity or disruption to your operations. Flexible engagement options mean our services adapt to your compliance requirements, project timelines, and business needs.
|
|
|
COMPLIANCE READY If you’re working toward compliance or preparing for an audit, our comprehensive reports highlight security weaknesses and provide the clarity and documentation you need for certifications and vendor assessments. |
|
|
|
PEACE OF MIND Know your systems are tested by experienced cybersecurity professionals using industry-standard methodologies. You’ll receive clear, actionable recommendations—no jargon, just practical steps to reduce risk. |
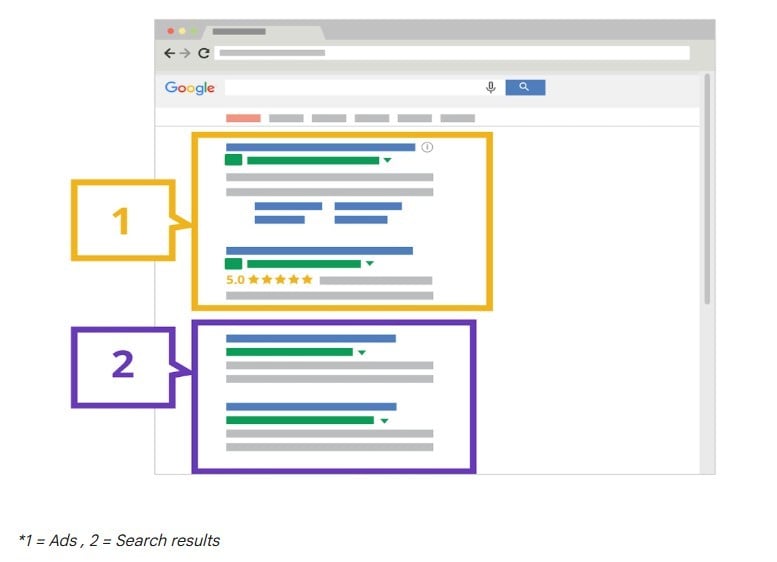
Sponsored Google search results: How scams and look‑alike ads can affect your business
Think the top Google result is always the safest? Not necessarily. Sponsored search ads are increasingly being used to impersonate legitimate businesses or divert traffic through look‑alike ads. We break down how it works, why it matters, and what Australian business owners should watch for.

Social Media scams explained: What Australian businesses should be aware of
Social media is a crucial part of how many Australian businesses market, sell and support customers - which also makes it an attractive target for scammers. From fake “Meta support” messages to full business account takeovers, these attacks are on the rise. In this article, we break down how social media scams work, real Australian examples, and the practical steps SMBs can take to better protect their accounts.
.png)
What Are DKIM and DMARC – and Why They Matter for Business Email Security
Most email scams don’t start with a virus or a hacked system - they start with an email that looks legitimate. DKIM and DMARC are two simple but powerful controls that help protect your business from impersonation, phishing and email fraud. Here’s what they are, how they work, and why they matter.