We had another very early start to the day recently with a call from a Manufacturing client on the Southside.
The day kicked off just before 6am- the reason? A number of files on their server were locked, making them in accessible to draftsmen, office staff and their CNC machines, effectively stopping their production dead.
The culprit was Veracrypt a new variant of the Crysis ransomware that’s been out in the wild for about 3 months. We located the entry point of the virus, the hackers logged in remotely to their environment through an internet facing windows computer using a genuine users name and password discovered through a dictionary attack.

As good fortune would have it, a business continuity device was already deployed onsite a month previous, allowing for the restoration of the files, but the damage was estimated at $37,000 in lost productivity and restoration expenses.
We took all their computers off the network and sanitized them one at a time before bringing them online. After that we made the necessary changes to their password policy and provided a VPN to ensure no open services to the internet. They are currently implementing improved security processes including Endpoint Detection and Response software, Multifactor Authentication along with ongoing Security Awareness Training for their users.
They were back up and running the next day, but it is just another timely reminder of the need for staff education on cyber security the
benefit of having the right security practices and business continuity solutions in place and regular auditing to ensure your business is
protected.
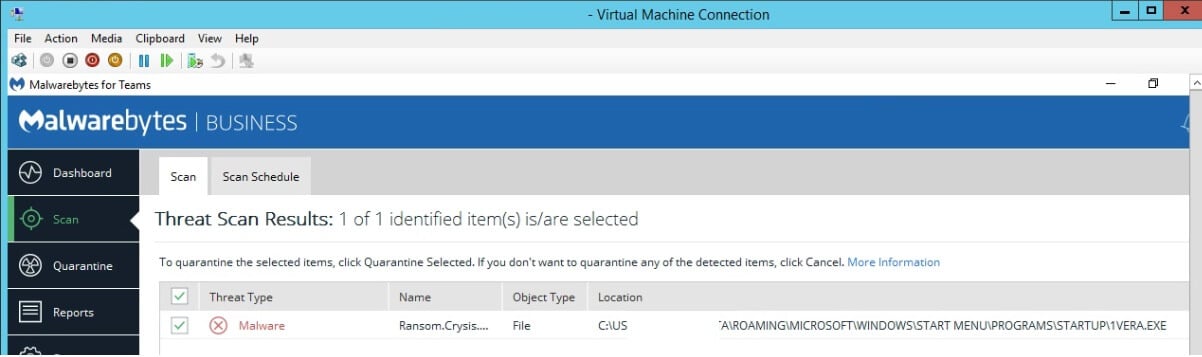 Scan
results undertaken as part of the audit process.
Scan
results undertaken as part of the audit process.