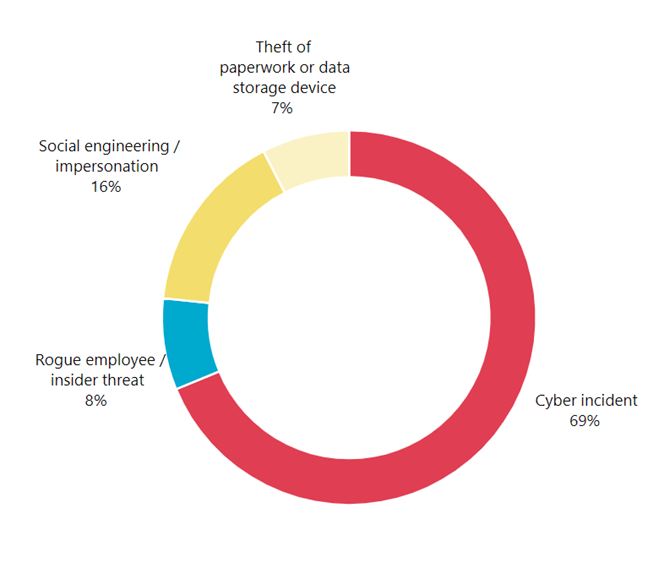
With Malicious or criminal attacks were the largest source of data breaches notified to the Office of the Australian Information Commissioner (OAIC) between January and June 2020, accounting for 317 breaches, the need for organisations and their staff to be ever vigilant about cyber security continues.
 Today, David hosted another webinar on behalf of the College of Law's Centre for Legal Innovation covering the Dark Web and how to provide
another line of defence in Cyber Security through Security Awareness Training for your staff.
Today, David hosted another webinar on behalf of the College of Law's Centre for Legal Innovation covering the Dark Web and how to provide
another line of defence in Cyber Security through Security Awareness Training for your staff.
In the Legal sector, cyber incidents and social engineering were the only attack vectors reported to OAIC during January to June 2020, highlighting them as a target for external threats such as phishing attacks and compromised credentials.
You can certainly put in place measures such as spam filters and firewalls to reduce the risk of an external attack, but what happens when the threats do get through?
This is where providing Security Awareness Training for your staff comes in and with the median annual return on investment of Security
Awareness Training being 5 times, it really is a no-brainer.
What is the Dark Web?
In simple terms, the Dark Web consists of unlisted and unknown websites (don’t bother Googling for them) that are heavily used
for criminal activities, whilst there are some legitimate business uses for it, you can be almost certain that if your information is on
the Dark Web, it is not good news. Check
out one of our previous blogs
for a deeper dive into the underbelly.
So, what illegal things are for sale on the dark web? Drugs top the list, but after that, there are 4 other main categories: Personal Data,
Financial Data, Guides & Templates and Software and Fraud service.
Personal data
Vendors sell everything from music-streaming accounts to credit reports, health records to full identity kits containing complete sets of personal and financial information.
Some fraudsters also openly leak Personally Identifiable Information (PII) — free for anyone to use or exploit. Long lists of usernames and passwords, email addresses or contact information float freely around the dark web.
Financial data
Financial data on the dark web typically appears as payment card information, banking information or payment processor accounts
Vendors typically safeguard full card numbers until after buyers make a purchase, and any fraudster in possession of financial data would extract all monetary value from the accounts before sharing remaining details with the broader fraud community.
Guides and templates
Guides contain detailed instructional kits for fraudsters that offer step-by-step tutorials on popular fraud schemes, including phishing, account takeover, business email compromise, tax fraud and how to cash out on stolen payment cards.
Some guides offer exclusively technical information, but many also provide recommendations for the social engineering aspects of fraud, such as how to speak to customer service representatives, managers, bank tellers and other associates they might need to interact with over the course of their fraud scheme.
Software and fraud service
Phishing schemers buy pre-made scam pages to convince users they’re visiting a legitimate website. These scam pages come loaded with the technology needed to capture account details when unsuspecting users interact with the page.
One vendor selling Personally Identifiable Information offered an additional look-up service, for a fee, if users wanted to track down the drivers’ license numbers for stolen identities they’d purchased. These value-add services expand a vendor’s potential profit.
But the Dark Web isn’t all guns and ID theft, with 2017 research by Terbium Labs showing that 47.7% of site content across TOR (one of the Dark Web capable browsers) hidden services is legal. This can range from media content, work by the international free press, and medical services or community groups, even The New York Times and Facebook have their own presence on the Dark Web.
How are they getting the data?
Criminals are relying on people to make mistakes, there are many ways that they are access the data for sale on the Dark Web and here are a
just a few:
Phishing and spear phishing
This might be an email requiring urgent action, tricking a user into clicking on a malicious link, or a more targeted spear-phishing attack where a fraudster impersonates the organization’s IT manager and contacts a specific individual requesting a password update.
Business Email Compromise (BEC)
An online scam where the fraudster impersonates a trusted business representative to trick an employee, a vendor or a client into revealing personal information, or even transferring funds to the attacker.
Ransomware
A malware program, typically a trojan, infects a device through a visit to a compromised website, or via a phishing email. Users are prevented from accessing their systems or data through encryption. Cybercriminals then use this to leverage financial gain from the affected person or business.
Baiting
An effective method of installing malware, baiting uses physical media (flash drives, optical drives) that have been infected with malicious software. Cybercriminals leave these items in public spaces frequented by their targets such as cafes, bathrooms or car parks, hoping an employee may find and use the device, thereby unknowingly installing malware on their workstation.
Vishing and Smishing
Derivatives of phishing, smishing, and vishing are types of social engineering fraud where the attacker uses either SMS messaging (smishing) or a phone call (vishing) in an attempt to gain access to private personal or financial information. As with phishing, these methods also rely on creating a sense of urgency in the victim in an attempt to obtain their personal data.
Malware
Trojans are typically sent via email; however, they can also be downloaded through a visit to an infected website and require an action by their victim to take effect. A popular trojan is one which masquerades as an antivirus program which, when run by the unsuspecting user, attacks, and damages their device and steals information.
How can Security Awareness Training help?
Spam filters and network protection such as firewalls can stop the majority of attempted attacks before they reach your organisation, but as
67% of current malware is zero day, this means that the filters aren’t even aware the threat exists and therefore cannot mitigate it. This
is where your next best line of defence is your staff.
Investing in Security Awareness Training (SAT) for your organisation on a monthly basis can reduce the risk of an attack, computer-based training is by far the most popular way to deliver it to staff with 79% of organisations using this delivery method. Training can be anything from a questionnaire to an in-person training session and is best led from the top, we encourage our clients hold regular discussions within the business about cyber security and to have an open door policy allow anyone to raise issues or report a breach without fear of repercussions.
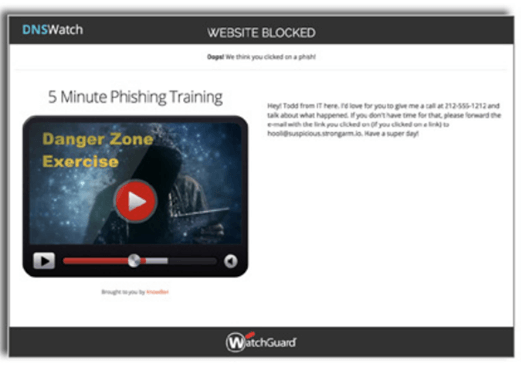
At FortiTech, we also recommend augmenting SAT with simulated phishing attacks to test the effectiveness of training and allow you to tailor it further. We conduct this on a monthly basis for our SAT clients and couple this with WatchGuard’s DNSWatch software, which, when triggered by a known phishing site blocks access to the site and then automatically plays a training video to educate the user on the dangers of phishing scams.
Our Top Tips
- Lead from the top – make sure to hold regular discussions within the business
- Build a culture of security awareness
- Implement safeguards such as WatchGuard DNSWatch
- Invest in security awareness training for your staff, it can pay for itself 5-fold
- Enrol your organisation in a Dark Web Monitoring service, they alert you to any instances of compromised credentials becoming available for sale on the Dark Web, allowing you to take action - our FortiTech monitoring service is just $50 + GST per month, per domain.
The threat of a data breach or lost information doesn't need to be a stressful situation, instead, with the right tools and guidance you can secure your organisation and turn your staff into Dark Web defenders. If you need help with where to start, give us a call on 1300 778 078 and we can help you out on your journey.