FortiTech continues to spread the word about the importance of Cyber Security and with that, David was joined by Matthew See, WatchGuard’s
Manager of Sales Engineering – APAC, hosting a webinar in conjunction with the College of Law's Centre
for Legal Innovation,
focusing on Patching and IoT.
David and Matthew covered 3 specific sections which we will run through below:
- What is IoT?
- Benefits of patching
- Ways to protect your organisation
What is IoT?
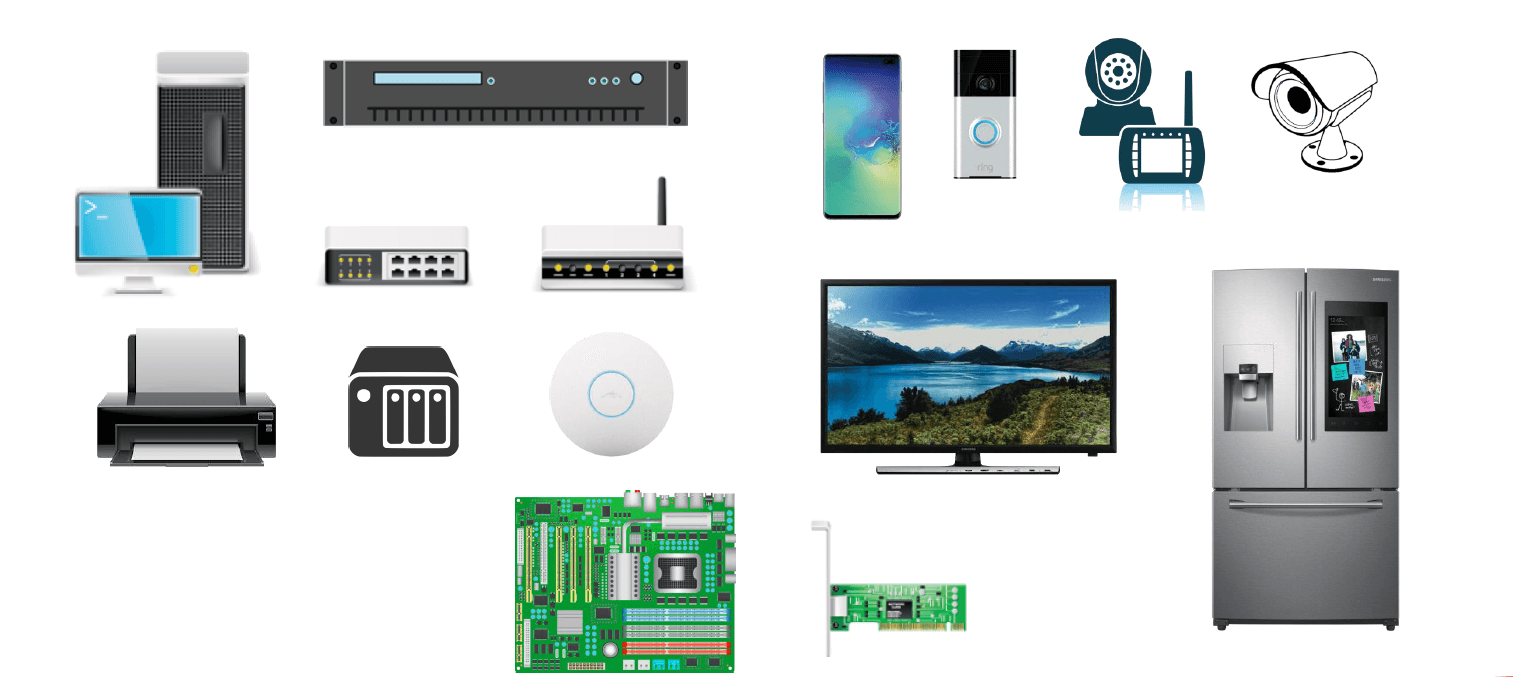
IoT or the Internet of Things, is all the other computing products that you have when you think of computers, this is a whole raft of
things, smart TV’s, Google Home & Alexa, switches, router, blu ray players, printers/scanners, security cameras and even fish tank
thermometers.
IoT can be broken down into a number of sectors:
E.g. light fixtures, home appliances, and voice assistance for the elderly.
Applications of IoT in the healthcare and transport industries, such as smart pacemakers, monitoring systems, and vehicle to vehicle communication (V2V)
Includes digital control systems, statistical evaluation, smart agriculture, and industrial big data.
Enables the connectivity of smart cities through the use of infrastructure sensors, management systems, and user-friendly user apps.
Application of IoT technologies in the military field, such as robots for surveillance and human-wearable biometrics for combat.
Medical Equipment such as pacemakers, respiratory devices, sensors and monitoring apps is the fastest growing area for IoT, meaning that
keeping it secure is paramount.
Alarmingly, 61% of organisations have experienced an IoT security incident and with the use of IoT devices is accelerating and expected to reach 21.5 billion in 2025.
With 60% of network breaches involved vulnerabilities for which a patch was available, but not applied the importance of patching your
devices is highlighted. But, what is patching?
The Benefits of Patching
A patch is a software update for a program or device aimed to improve its functionality or fix a security flaw.
Manufacturers often find there are issues with their products through customer feedback or a security incident and will then develop patches to remedy it. Updating your firmware and patching software regularly means that you are limiting your exposure to a possible attack.
Here are just a few items that require regular patching:
For IoT devices, the risk also extends to the networks to which the devices are connected as these devices can easily serve as the gateway of choice for hackers to penetrate a network.
Take “SweynTooth,” for example, which allows a hacker to take control of an IoT device or stop it from working by exploiting vulnerabilities in third-party code. The SweynTooth attacks affect a broad range of Bluetooth Low Energy devices, including many consumer devices and some medical devices.
Finding security vulnerabilities is big business
Software and hardware developers want to ensure their products are secure and often run open bounty programs allowing members of the
public, mainly ethical hackers to attempt to exploit security vulnerabilities in their products, log the vulnerability and collect a
monetary reward.

Microsoft Bug Bounty Program offers monetary rewards for security researcher that have found a vulnerability in a Microsoft product,
service, or device
Bounties range from USD15,000 for Microsoft Edge vulnerabilities up to USD250,000 for Microsoft Hyper-V.
Microsoft Patch Tuesday – Generally the second and sometimes fourth Tuesday of the month, though they have also released emergency patches as well.
For the year to date 860 patches have been released by Microsoft

Group of 750,000 Ethical Hackers offering services to corporates to test their products for vulnerabilities, they do this through a range of
platforms including private programs, events and competitions
Hackerone are so well organised they provide benchmarks and analytics including reports on ROI
This has become an industry for people who have the skills to hack to do it for the right side.
Organisations such as PayPal, Hyatt Hotels, Shopify, Uber, GooglePlay use them
Patch Management Best Practices
- Audit the operating systems and applications software you have
- Assess potential vulnerabilities in your environment
-
Establish:
- A compliance program
- A regular maintenance schedule
- Product owners
- Change control processes
- Review and assess patch releases
Determine if a newly released patch is relevant to your current environment, if not then document it and ignore it.
If a security patch is release, determine if it is Critical or whether it could it be exploited? If yes, then schedule it for rollout ASAP.
Regulatory Compliance can also come into consideration as you decide whether a patch needs to be rolled out.
If you are looking to deploy a patch or software update, always ensure to deploy in test environment first. This will allow you the opportunity to determine how it will behave in your network and give you time to test, review, update processes and documentation. Once this is all verified then you can deploy to the rest of the network.
99.96% of active vulnerabilities in corporate endpoints are due to missing updates, 86% is due to unpatched 3rd party applications and unsupported End of Life (EOL) software such as Windows 7 is a common problem.
Tips
- Identify everything on your network, not just computers and servers
- There are a number of businesses who can scan and identify all the assets on your network
- Make sure your devices are patched regularly – especially for security fixes
- And if they can’t be patched, make sure they are segregated on your network. Invest in a firewall to allow you to do this, it will reduce the risk of a threat spreading
- Engage a professional that manages your patching as part of an overall security framework.
With the right tools and regular patching and software maintenance you can secure your organisation or personal devices with ease. If you
need help with where to start, give us a call on 1300 778 078 and we can help you out on your journey.